Google Threat Intelligence Group, in collaboration with Google DeepMind, has issued a stark warning about the operationalization of artificial intelligence by cybercriminals. Their latest assessment underscores that AI is not necessarily creating new types of attacks but is significantly enhancing the efficiency, precision, and reach of existing methods. This development is alarming as it indicates a shift in how threats are executed.
The report indicates that large language models are facilitating a faster transition from concept to execution in cyberattacks. During the reconnaissance phase, adversaries can leverage publicly available data to create detailed profiles of executives, vendors, and technical vulnerabilities, allowing them to strategize their attacks with remarkable clarity.
In the realm of social engineering, AI is proving instrumental in generating convincing narratives, emails, and identities specifically tailored to deceive individual targets. Concurrently, malware developers are employing generative tools to refine exploits, investigate evasion strategies, and rapidly produce new variants, which pose a considerable challenge to traditional cybersecurity measures.
Researchers are also tracking the emergence of malware that consults AI services in real time during attacks. Such threats are capable of dynamically generating commands, altering their behavior on the fly, and accelerating data exfiltration, thus circumventing established detection mechanisms.
The 2026 report identifies several specific malware families utilizing AI APIs during execution to enhance their stealth and automate data theft. Among these, HONESTCUE operates as a downloader and launcher, using the Gemini API to dynamically create C# code in memory, facilitating its execution while evading static analysis tools. Meanwhile, PROMPTFLUX, a VBScript dropper, rewrites its source code hourly, creating a recursive cycle of mutation that helps it evade signature-based detection methods.
Another notable example is PROMPTSTEAL, an infostealer that queries large language models to generate system commands on demand, thus replacing traditional hard-coded instructions that are easily flagged. The COINBAIT phishing kit employs AI to clone cryptocurrency exchange interfaces with high visual fidelity, thereby enhancing its efficacy in harvesting user credentials. Additionally, Xanthorox has emerged as a dark web service marketed as a custom “offensive AI,” essentially a rebranded wrapper for legitimate commercial language models designed to bypass safety filters.
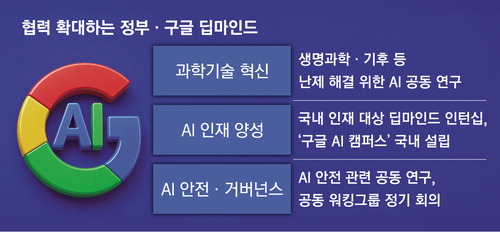
Activity associated with groups like APT28 highlights how automation is not only enhancing individual attacks but is also being employed to support broader geopolitical objectives by enabling sharper targeting and scalable intelligence gathering. A rising concern among cybersecurity experts is the tactic known as model distillation, where attackers flood systems with structured prompts in an attempt to replicate proprietary reasoning, essentially copying intelligence rather than merely data.
Google advises organizations to treat AI agents as legitimate identities, advocate for stringent privilege management, and implement defenses capable of responding at machine speed. In a landscape where every millisecond counts, relying solely on manual security measures is no longer viable.
While AI is undeniably driving innovation across various sectors, it is simultaneously redefining the cybersecurity threat landscape. The implications of these developments necessitate a reevaluation of existing security frameworks to ensure they can withstand the increasingly sophisticated tactics employed by cyber adversaries.
See also Gen Digital Launches Gen Agent Trust Hub to Bolster AI Security Amid Scam Threats
Gen Digital Launches Gen Agent Trust Hub to Bolster AI Security Amid Scam Threats SentinelOne Launches New AI Data Security Tools Amid 44% Shareholder Value Decline
SentinelOne Launches New AI Data Security Tools Amid 44% Shareholder Value Decline Network Security Monitoring Enhances Threat Detection Speed by 30% with Full Packet Capture
Network Security Monitoring Enhances Threat Detection Speed by 30% with Full Packet Capture South Korea’s Cybersecurity Investment Stagnates Despite 26% Rise in Attacks
South Korea’s Cybersecurity Investment Stagnates Despite 26% Rise in Attacks Cato Networks CEO Shlomo Kramer Reveals Key Investment Criteria for AI Startups
Cato Networks CEO Shlomo Kramer Reveals Key Investment Criteria for AI Startups