IBM’s latest X-Force Threat Intelligence Index indicates a significant rise in cyberattacks stemming from basic security vulnerabilities, as attackers increasingly leverage AI tools to identify and exploit these gaps more swiftly. The report identifies the Asia-Pacific region as the second most-targeted, accounting for 27% of cases monitored by IBM X-Force.
This surge in cyber threats comes at a time when regional governments and organizations are grappling with risks to critical infrastructure. In Singapore, all four telecom operators were recently targeted by the threat actor known as UNC3886, prompting what has been described as the nation’s largest coordinated cyber response. Alongside the index, research from Thales and S&P Global 451 Research reveals that 71% of organizations in the Asia-Pacific region now consider AI their foremost data security risk.
Globally, attacks initiated through the exploitation of public-facing applications increased by 44%. IBM attributes much of this growth to absent authentication controls and AI-aided vulnerability discovery. In 2025, vulnerability exploitation emerged as the leading cause of attacks, comprising 40% of incidents recorded in the X-Force observations.
The index also highlights a more crowded landscape for ransomware. IBM reported a 49% year-on-year increase in active ransomware and extortion groups, with publicly disclosed victim counts rising approximately 12%. The ransomware ecosystem has become more fragmented, characterized by smaller, transient operators conducting lower-volume campaigns, complicating attribution efforts.
This shift is partly driven by the reuse of leaked tools, established playbooks, and AI that automates various operational aspects. Mark Hughes, Global Managing Partner for Cybersecurity Services at IBM, noted, “Attackers aren’t reinventing playbooks; they’re speeding them up with AI.” He emphasized that while the core challenge remains the same—businesses are overwhelmed by software vulnerabilities—the pace of exploitation has accelerated. With many vulnerabilities requiring no user credentials, attackers can swiftly transition from scanning to impact without human intervention. Security leaders are urged to adopt a more proactive approach, utilizing AI-powered threat detection and response to identify vulnerabilities and mitigate threats before they escalate.
In the Asia-Pacific, malware was the primary method of attack, comprising 45% of observed activities, followed by spam and the use of legitimate tools at 15% each, and server access at 10%. The exploitation of public-facing applications and the use of valid accounts were the leading vectors for initial access in the region, at 50% and 30%, respectively. IBM regards these trends as indicators of weaknesses in managing internet-facing exposure and protecting identities and credentials.
Data theft and damage to brand reputation were reported as the most significant impacts of cyberattacks in the region, each accounting for 14%, while credential harvesting represented 7%. Catherine Lian, General Manager and Technology Leader at IBM ASEAN, stated, “Asia-Pacific continues to face a sharp increase in cyber threats, with attackers increasingly leveraging AI and exploiting gaps in basic security.” She emphasized the necessity for organizations to focus on identity protection, securing configurations, and ensuring visibility across cloud and application environments to stay ahead of evolving, automated threats.
For the fifth consecutive year, manufacturing has emerged as the most targeted industry, representing 27.7% of incidents recorded by X-Force. Data theft was the most common outcome in this sector. Notably, Asia-Pacific accounted for 68% of all manufacturing-related incidents, with manufacturing comprising 65% of targeted sectors, followed by finance and insurance at 17% and transportation at 7%.
The index also sheds light on identity risks associated with workplace AI services. IBM’s X-Force reported that infostealer malware led to the exposure of over 300,000 ChatGPT credentials in 2025, indicating that AI platforms are now facing credential risks akin to those of other widely adopted software-as-a-service tools. The risks associated with compromised chatbot credentials extend beyond mere account access, potentially leading to output manipulation, data exfiltration, and malicious prompt injections. IBM suggests that strong authentication and conditional access controls are essential for mitigating such exposures.
In addition to endpoint and identity-driven attacks, supply chain compromises have emerged as a growing concern. X-Force noted a nearly fourfold increase in significant supply chain or third-party breaches since 2020, linking this trend to attackers exploiting established trust relationships, development automation, and software-as-a-service integrations. IBM also highlights a narrowing gap between nation-state and financially motivated actors, observing that the tactics and techniques have proliferated across underground forums. AI is streamlining both reconnaissance and exploitation, with methods traditionally associated with state-backed groups now appearing more frequently among profit-driven entities. As AI coding tools enhance software output, pressure on development pipelines and open-source ecosystems is expected to escalate further in 2026, potentially introducing unvetted code into workflows.
See also Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism
Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage
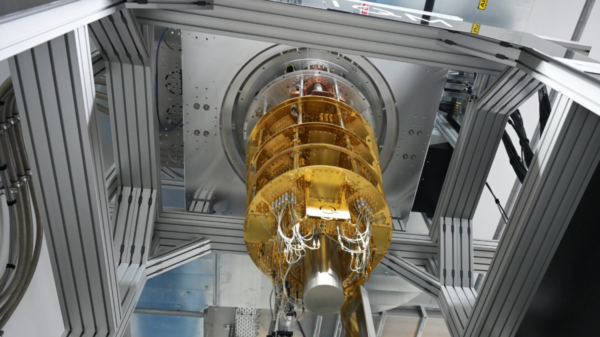
Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage Quantum Computing Threatens Current Cryptography, Experts Seek Solutions
Quantum Computing Threatens Current Cryptography, Experts Seek Solutions Anthropic’s Claude AI exploited in significant cyber-espionage operation
Anthropic’s Claude AI exploited in significant cyber-espionage operation AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks
AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks