The Trump administration’s 2025 cybersecurity reset seeks to reduce federal oversight while sharpening its focus on foreign threats and critical technologies. Issued in June, the executive order aims to strengthen national cybersecurity, fulfilling a key campaign promise, by maintaining the existing federal framework but redirecting priorities toward artificial intelligence, post-quantum cryptography, and countering foreign actors. This shift offers clearer guidance for federal technology efforts but proposes significant funding cuts that may undermine overall cybersecurity resilience.
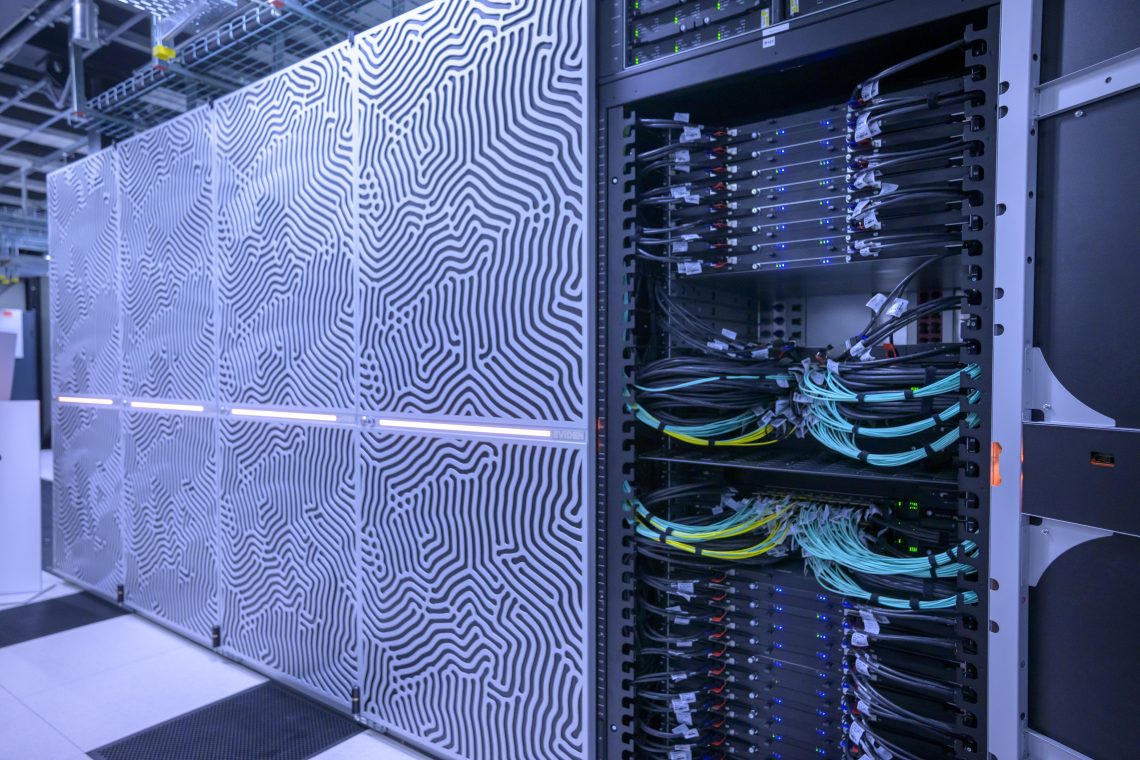
The draft 2026 budget reveals a proposed 17 percent reduction for the Cybersecurity and Infrastructure Security Agency (CISA), along with the elimination of over 1,000 positions and nearly $495 million in funding. The Office of the Director of National Intelligence faces even steeper reductions, risking diminished capacity to combat frequent cyberattacks from state-linked actors and ransomware groups. The dismantling of Russian intelligence desks within U.S. agencies further limits the government’s ability to track and counter foreign espionage and disinformation campaigns.
The recent “Signalgate” episode has highlighted human vulnerabilities in cybersecurity, as Defense Secretary Pete Hegseth reportedly utilized an unclassified Signal group chat to share sensitive details of U.S. airstrikes with aides, journalists, and family members. Such behavior increases the risks of surveillance and exploitation, particularly when officials connect to foreign networks during international travel.
The international cyber threat landscape is rapidly evolving, as the use of AI in cyber operations enhances the scale and sophistication of attacks. Malicious actors now leverage AI for faster, more adaptive intrusions, impacting both offensive and defensive strategies in hybrid warfare. However, private operators of critical infrastructure hesitate to adopt offensive capabilities due to potential legal repercussions and attribution challenges, keeping such initiatives primarily within government and military frameworks.
This reality has led to discussions about establishing a dedicated military cyber force as a new branch of the armed forces. Proponents argue that ongoing attacks from China, Russia, Iran, and North Korea necessitate a specialized military response. Since its invasion of Ukraine in 2022, Russia has escalated cyber operations targeting U.S. critical infrastructure, prompting calls for broader use of offensive cyber measures to deter attacks on essential services.
In response to state-sponsored cyber activity, the U.S. has primarily relied on sanctions and diplomatic pressure, while attempting to coordinate technology governance with allies. Despite these efforts, adversaries like China continue to enhance their cyber arsenals, increasingly shifting from espionage to acts of sabotage.
The financial repercussions of cyberattacks have surged, with U.S. state and local governments now facing average costs of $2.8 million to $9.5 million per incident. Ransomware has emerged as the fastest-growing form of cybercrime, with incidents multiplying fivefold over the past five years. The healthcare sector has been particularly hard-hit, accounting for about one-fifth of all cases in the U.S. between 2014 and 2024, underscoring the urgent need for improved cybersecurity measures.
China has positioned itself as the leading state-sponsored cyber adversary, increasingly employing AI tools for malicious activities. Notable incidents include the “Salt Typhoon” group’s breach of nine U.S. telecommunications firms, which granted access to sensitive geolocation data. Despite a substantial cybersecurity budget, the U.S. Treasury Department’s systems were compromised for over a year, highlighting vulnerabilities in federal networks.
As the threat from Iranian and North Korean hackers intensifies, the need for renewed focus on U.S. cybersecurity has become apparent. While some posit that the Trump administration’s recalibrated policy might enhance focus on high-end threats, critics warn that budget cuts, politicization, and weakened alliances could have detrimental effects on national security.
The potential for diminished information sharing between the U.S. and its allies raises further concerns. The administration’s more transactional approach to digital regulation may hinder cooperation with European initiatives, compromising collective leverage on cyber norms. As cyberattacks on critical infrastructure escalated by 668 percent between 2020 and 2024, trust among allies has been eroded, complicating transatlantic collaboration.
Ultimately, the administration’s current policy may strengthen focus on state actors and advanced persistent threats but risks leaving gaps in coverage against lower-profile attacks. The balance between offensive and defensive capabilities must be carefully managed to maintain the integrity of U.S. cybersecurity. The efficacy of these new policies will depend significantly on Congress’s willingness to preserve funding for critical cybersecurity efforts, ensuring that state and local governments are equipped to face the escalating threat landscape.
See also Chinese Hackers Use Anthropic’s Claude AI for 90% of Major Cyberespionage Campaign
Chinese Hackers Use Anthropic’s Claude AI for 90% of Major Cyberespionage Campaign Microsoft’s Digital Crimes Unit Targets AI-Driven Cyber Threats with $20B Strategy
Microsoft’s Digital Crimes Unit Targets AI-Driven Cyber Threats with $20B Strategy First Trust NASDAQ CEA Cybersecurity ETF Surpasses $11B in Assets by 2025
First Trust NASDAQ CEA Cybersecurity ETF Surpasses $11B in Assets by 2025 Jeffs’ Brands Announces Exclusive MOU to Distribute AI-Powered Security Systems in Key Markets
Jeffs’ Brands Announces Exclusive MOU to Distribute AI-Powered Security Systems in Key Markets