Cybercriminals are infiltrating compromised systems at an alarming pace, with a recent analysis from CrowdStrike revealing that the speed of cyber intrusions is increasing dramatically. The 2026 Global Threat Report highlights a particularly concerning statistic: one attack was documented moving across a network in as little as 27 seconds, underscoring the urgent need for organizations to enhance their cybersecurity measures.
The report defines ‘breakout time’ as the interval between the initial breach of a system and the subsequent lateral movement to other devices within the network. In 2025, the average breakout time for financially motivated cybercriminals plummeted to just 29 minutes, marking a significant decrease from prior years. The fastest recorded instance, however, was a mere 27 seconds, suggesting that skilled attackers can quickly navigate from one compromised endpoint to additional systems if defenses are not automated and real-time.
Experts emphasize that this shrinking window for detection highlights the critical importance of early identification of threats. Once attackers initiate lateral movement, they can escalate privileges, access sensitive data, or deploy ransomware before most security teams are even alerted to the intrusion.
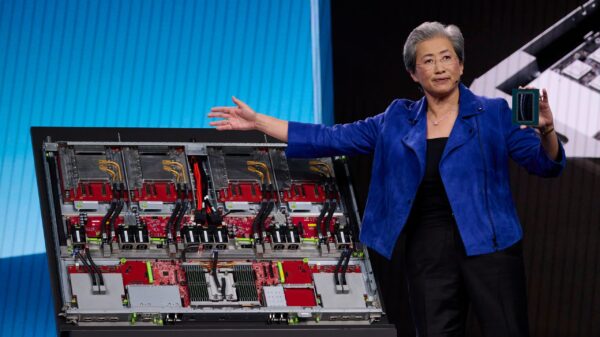
Another worrisome trend identified in the report is the growing role of artificial intelligence in cyber operations. Cybercriminals are increasingly utilizing AI to automate reconnaissance and generate malicious scripts, leading to an 89% rise in operations conducted by AI-enabled adversaries compared to the previous year. Furthermore, there is a new risk wherein AI systems themselves are becoming targets. Attackers have been noted injecting harmful prompts into generative AI tools to produce commands that facilitate credential theft and the exfiltration of digital assets. Some vulnerabilities in AI development platforms have even been exploited to maintain ongoing access within compromised environments.
The report warns that as businesses widely adopt AI technologies, the overall attack surface expands, presenting new opportunities for criminals and nation-state hackers alike. Cyber operations are increasingly blending into normal activity, leveraging legitimate services and trusted systems. Most intrusions now occur through cloud platforms, SaaS solutions, and compromised identities, making it more difficult to identify malicious traffic. Researchers found that sensitive data could start leaving a victim’s environment within minutes of initial access, illustrating how swiftly attackers can act once inside a network.
According to cybersecurity experts, the rapid advancements in automation, AI, and cloud-based infrastructure are fundamentally altering the landscape of cyberattacks. Traditional security measures that rely heavily on manual investigations are becoming less effective against these accelerated threats. Experts suggest that organizations must implement constant monitoring, automated detection systems, and faster response capabilities to keep pace with modern attacks.
The central message of CrowdStrike’s report is unmistakable: cybersecurity is now a race against time. As the timeline of an intrusion compresses from hours to mere minutes—and in some instances, seconds—the margin for error continues to diminish. For businesses and government agencies, the implications are dire. If systems are not designed for real-time threat detection and response, attackers may already have infiltrated and spread across the network before security teams can react.
This evolving threat landscape necessitates a shift in how organizations approach cybersecurity, making it imperative to stay ahead of increasingly sophisticated tactics employed by cybercriminals. The rapid pace of modern cyber threats calls for a proactive rather than reactive stance, emphasizing the need for continuous improvement in security protocols and technologies.
See also Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism
Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage
Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage Quantum Computing Threatens Current Cryptography, Experts Seek Solutions
Quantum Computing Threatens Current Cryptography, Experts Seek Solutions Anthropic’s Claude AI exploited in significant cyber-espionage operation
Anthropic’s Claude AI exploited in significant cyber-espionage operation AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks
AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks