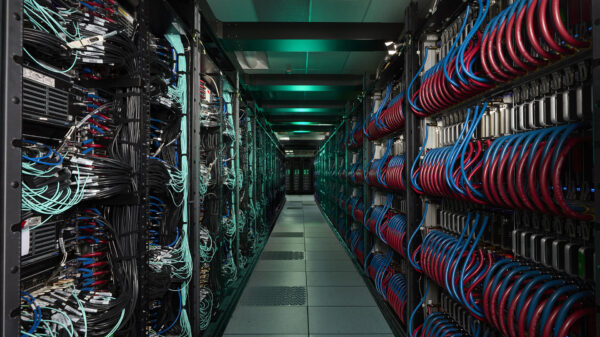
Latin America is increasingly becoming a focal point for cybercriminal activities, now accounting for 9% of all global cyberattacks, according to IBM. This uptick reveals a concerning trend of automated exploitation, credential theft, and the emerging risks associated with shadow AI. Mexico, in particular, faces heightened vulnerabilities across pivotal sectors including financial services, energy, and manufacturing, where outdated systems and the convergence of Information Technology (IT) and Operational Technology (OT) pose significant challenges to regulatory compliance and digital resilience.
The region remains the fifth most targeted globally, with a rise from 8% of total cyberattacks in 2024 to 9% in 2025. The IBM X-Force Threat Intelligence 2026 report outlines four primary vectors driving this increase: exploitation of public applications, use of valid accounts, compromise of remote services like VPNs, and supply chain intrusions—each demonstrating a 25% effectiveness rate. The report highlights a notable shift in methodologies, with attackers increasingly leveraging legitimate administrative tools for malicious purposes. Approximately 33% of incidents involved the use of software already present within corporate environments, such as Microsoft Teams and various scripting tools, complicating detection efforts for cybersecurity teams.
The financial and insurance sectors have historically been prime targets, yet the energy and manufacturing industries are now experiencing a significant spike in cyber incidents. These sectors accounted for 47% and 27% of major incidents, respectively. As IT and OT converge, the attack surface expands, especially in manufacturing, making legacy systems particularly vulnerable. According to IBM, there has been a 44% increase in the exploitation of software vulnerabilities. While “zero-day” vulnerabilities often capture the most attention, threat actors are increasingly focused on “n-day” vulnerabilities—known flaws with existing patches that remain unaddressed for years. The difficulty in updating legacy systems amplifies this risk, creating an opportunity for attackers.
Between 2024 and 2025, the number of identified vulnerabilities surged by 13,000, reaching a total of 40,000 within a single year. Attackers rationalize their efforts by determining that scanning for unpatched vulnerabilities—some dating back a decade—yields a better return on investment than discovering new exploits. Compounding this issue is the rising complexity of supply chains, which has made supply chain attacks a favored method of intrusion, increasing nearly fourfold over the past five years. Organizations often prioritize internal security but neglect to monitor third, fourth, or even fifth-party risks, leaving them susceptible to exploitation through weaker links in their supply chains.
Rodolfo Manzi, Security Services Leader at IBM Mexico, emphasizes this vulnerability, stating, “Even if a primary corporation is mature and well-protected, its vendors or service providers may lack equivalent controls.” The trend of targeting open-source libraries has also emerged, as attackers embed malicious code into libraries available through platforms like NPM or Maven. When corporate developers integrate these libraries, they inadvertently introduce threats into their internal environments.
AI technology presents additional risks, particularly in terms of identity theft and data exposure. Research indicates that over 300,000 credentials for AI platforms, including ChatGPT, have surfaced on the dark web. As employees increasingly turn to unapproved AI tools to boost productivity, a phenomenon dubbed “Shadow AI,” the potential for credential theft escalates. Such compromises grant attackers access to sensitive corporate data and proprietary code, with one in six security incidents now linked to AI misuse or compromise. Furthermore, attackers are adapting their tactics in real-time using AI, modifying their attack patterns immediately if a specific intrusion attempt is thwarted.
The democratization of cybercrime tools has fragmented the ransomware market, with the number of major groups escalating from 10 in 2024 to 109 by 2025. This 49% increase is attributed to “ransomware-as-a-service” models and affiliate programs, lowering the barrier to entry for less experienced hackers. As such, smaller groups can now acquire sophisticated tools and share profits with original developers, intensifying the potential for high-impact cybercrime.
To combat these evolving threats, Manzi suggests that corporate leadership focus on four critical areas. First, organizations should treat digital identity as critical infrastructure, applying governance to user identities and AI agents similar to physical servers and networks. Second, reliance on monthly patch cycles is no longer adequate; continuous vulnerability management using AI-driven tools is essential to identify and remediate vulnerabilities across the attack surface. Third, companies should govern their AI platforms by providing sanctioned, secure tools for employees, coupled with strict data classification policies. Lastly, fostering a culture of cyber awareness and education is crucial; regular training can help employees grasp the risks of sharing sensitive information with unmonitored AI tools and the importance of multi-factor authentication.
The rapid integration of AI in corporate workflows presents both opportunities and challenges. Without appropriate governance and oversight, organizations risk extending their attack surfaces beyond the security department’s control. As Manzi concludes, “The goal for attackers is to maximize results with minimal effort.” To counter this, organizations must automate their defenses and secure every digital identity within their networks.
See also Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism
Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage
Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage Quantum Computing Threatens Current Cryptography, Experts Seek Solutions
Quantum Computing Threatens Current Cryptography, Experts Seek Solutions Anthropic’s Claude AI exploited in significant cyber-espionage operation
Anthropic’s Claude AI exploited in significant cyber-espionage operation AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks
AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks