In a week marked by significant cybersecurity developments, The Cyber Express has reported on a major supply chain disruption involving Stryker Corporation, alongside rising concerns about the security and legal risks associated with the rapid adoption of artificial intelligence (AI) technologies. These incidents occur against a backdrop of escalating cyber activity spurred by geopolitical tensions, emphasizing the urgent need for robust cybersecurity measures across industries.
The recent cyberattack on Stryker Corporation has resulted in notable disruptions to its manufacturing, shipping, and order processing operations. Although internal systems have been significantly affected, customer products remain unaffected. The attack, attributed to the Handala group, is under investigation by the Cybersecurity and Infrastructure Security Agency (CISA). The timeline for recovery remains unclear, raising concerns about the potential long-term impacts on the company’s supply chain integrity.
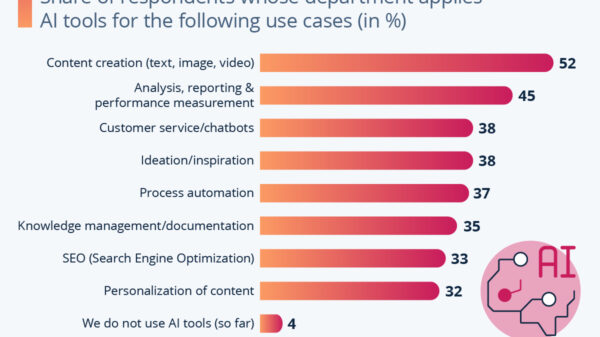
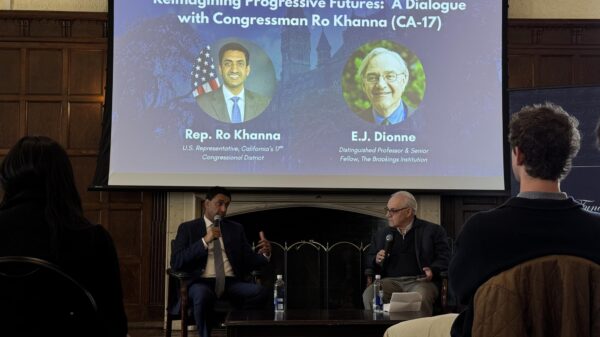
In the realm of AI, cybersecurity expert Lisa Fitzgerald has warned that the swift deployment of AI tools without adequate governance frameworks poses substantial risks to organizations. In a recent interview, Fitzgerald stressed that without structured risk assessments, employee training, and clear governance protocols, businesses could face data breaches, regulatory violations, and a loss of control over sensitive information. This caution underscores the necessity for companies to adopt comprehensive strategies as they incorporate AI into their operations.
Amid these concerns, Bonnie Butlin has highlighted the importance of collaboration in tackling complex cybersecurity threats. She advocated for dismantling industry silos and enhancing cross-sector cooperation to bolster resilience against evolving risks. Butlin emphasized that inclusive leadership models are essential for fostering a more cohesive approach to cybersecurity, particularly in a landscape where threats increasingly transcend organizational boundaries.
A recent U.S. intelligence report has identified China as the most persistent cyber threat actor, with operations reportedly embedded in critical infrastructure systems. This assessment also points to active cyber initiatives from Russia, North Korea, and Iran, each employing varied tactics ranging from espionage and sabotage to cybercrime and misinformation campaigns. The report indicates a pressing need for heightened vigilance among organizations managing critical infrastructure.
In the Middle East, escalating geopolitical conflicts have led to a surge in cyberattacks targeting critical sectors such as energy, finance, and communications. Cyble Research and Intelligence Labs have noted that these attacks are intensifying alongside ongoing regional tensions, marking a troubling trend in cyber warfare as nations increasingly leverage digital means to advance their geopolitical goals.
This week’s developments reflect the growing complexity of the global cybersecurity environment. The incidents involving Stryker and the escalating risks associated with AI governance underscore a critical imperative for organizations, governments, and individuals to remain vigilant. Emphasizing strong governance frameworks and proactive security measures, including timely patching and continuous monitoring, is essential for effectively navigating the fast-evolving threat landscape.
As organizations confront these multifaceted challenges, the need for coordinated defense strategies becomes ever more crucial. With the potential for disruption in supply chains and the rise of sophisticated cyber operations, businesses must prioritize operational resilience while fostering collaboration across sectors to mitigate risks. The current landscape demands not just reactive measures but also a forward-looking commitment to cybersecurity as a foundational element of organizational strategy.
See also Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism
Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage
Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage Quantum Computing Threatens Current Cryptography, Experts Seek Solutions
Quantum Computing Threatens Current Cryptography, Experts Seek Solutions Anthropic’s Claude AI exploited in significant cyber-espionage operation
Anthropic’s Claude AI exploited in significant cyber-espionage operation AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks
AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks