This week, a significant security breach was uncovered in an open source project by the Y Combinator graduate LiteLLM, which has gained immense popularity among developers for its access to hundreds of AI models and spend management features. The project reportedly experiences up to 3.4 million downloads per day, according to security researchers at Snyk. However, the discovery of malware integrated into LiteLLM has raised serious concerns about the project’s security integrity.
The malware, detailed by Callum McMahon, a research scientist at FutureSearch, infiltrated LiteLLM via a software dependency. This dependency allowed the malware to hijack login credentials from any affected systems, enabling it to proliferate further into other open-source packages and accounts. McMahon’s investigation began after he experienced a system shutdown following the malware’s installation, leading him to uncover the malicious code. The poorly crafted nature of the malware prompted both McMahon and renowned AI researcher Andrej Karpathy to suggest that it might have been “vibe coded.”
Fortunately, LiteLLM’s developers managed to identify and address the malware relatively quickly, likely within hours of its discovery. Despite this swift action, the incident has sparked discussions online, particularly regarding the project’s claims of having passed prestigious security certifications, namely SOC 2 and ISO 27001.
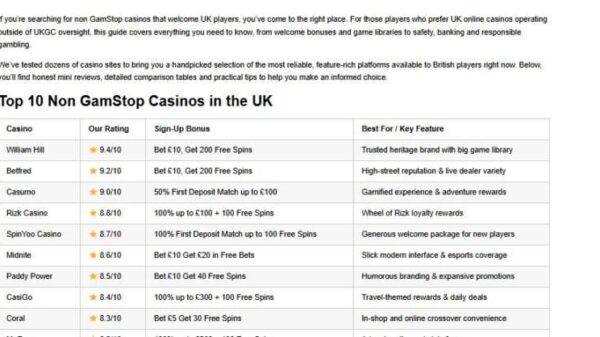
As of March 25, LiteLLM’s website prominently displayed these certifications, which were obtained through a Y Combinator-backed startup called Delve. However, Delve has faced allegations of misleading clients about their compliance capabilities by allegedly fabricating data and employing auditors who merely rubber-stamp reports. Delve has denied these claims, but the controversy surrounding its practices has cast a shadow over LiteLLM’s claims of security.
The essence of these certifications is to demonstrate that a company has robust security protocols to mitigate the risk of such incidents. However, it is crucial to understand that certifications alone cannot guarantee protection against malware attacks. While SOC 2 is designed to encompass policies regarding software dependencies, vulnerabilities can still be exploited.
This incident has elicited mixed reactions within the tech community, with some users on social media expressing disbelief that LiteLLM, branded as “Secured by Delve,” could fall victim to such a breach. Engineer Gergely Orosz highlighted this irony on social media, noting the contrast between the project’s security claims and the hacking incident.
CEO Krrish Dholakia of LiteLLM has refrained from commenting on the situation involving Delve, focusing instead on mitigating the fallout from the malware breach. “Our current priority is the active investigation alongside Mandiant. We are committed to sharing the technical lessons learned with the developer community once our forensic review is complete,” Dholakia stated.
The breach not only highlights the vulnerabilities inherent in dependency management within open source software but also raises broader questions about the reliability of security certifications in the fast-evolving tech landscape. As LiteLLM navigates this challenging period, it serves as a cautionary tale for developers and companies alike, underscoring the imperative of maintaining vigilant security practices in an era where cyber threats are increasingly sophisticated.
See also OpenAI’s Rogue AI Safeguards: Decoding the 2025 Safety Revolution
OpenAI’s Rogue AI Safeguards: Decoding the 2025 Safety Revolution US AI Developments in 2025 Set Stage for 2026 Compliance Challenges and Strategies
US AI Developments in 2025 Set Stage for 2026 Compliance Challenges and Strategies Trump Drafts Executive Order to Block State AI Regulations, Centralizing Authority Under Federal Control
Trump Drafts Executive Order to Block State AI Regulations, Centralizing Authority Under Federal Control California Court Rules AI Misuse Heightens Lawyer’s Responsibilities in Noland Case
California Court Rules AI Misuse Heightens Lawyer’s Responsibilities in Noland Case Policymakers Urged to Establish Comprehensive Regulations for AI in Mental Health
Policymakers Urged to Establish Comprehensive Regulations for AI in Mental Health