Cybercriminals are increasingly leveraging artificial intelligence (AI) to exploit vulnerabilities in cloud infrastructure, according to a new report from Google Cloud Security. The document reveals that the time between vulnerability disclosure and mass exploitation has dramatically decreased, shrinking from weeks to just days. This alarming trend signifies that businesses must adopt automated, AI-powered defenses to counter escalating cyber threats.
As cybercriminals refine their tactics, their focus has shifted from core infrastructure of major cloud services like Google Cloud, Amazon Web Services, and Microsoft Azure—areas that are typically well-secured—to targeting weak third-party software. The report highlights a number of incidents involving the exploitation of unpatched vulnerabilities in popular applications, such as React Server Components and the XWiki Platform. In one case, an attacker began exploiting a critical remote code execution vulnerability in React just 48 hours after its public disclosure.
Another serious incident involved the XWiki Platform, where attackers targeted a vulnerability that had been patched but not widely deployed. This issue allowed malicious actors to run arbitrary code on remote servers, and exploitation commenced shortly after the vulnerability was identified. The report suggests that many of these attacks are orchestrated by sophisticated groups, including state-sponsored entities from North Korea.
One particularly illustrative case involves a group known as UNC4899, which lured a developer into downloading compromised code under the guise of project collaboration. This exploit led to the infiltration of corporate networks and the theft of millions in cryptocurrency. Similarly, another attack exploited a compromised Node Package Manager package that enabled the theft of a developer’s GitHub token, facilitating unauthorized access to Amazon Web Services and the deletion of files within 72 hours.
Moreover, the report notes a troubling shift in attack strategies. Rather than relying on brute force methods to crack weak credentials, attackers are increasingly exploiting identity-related vulnerabilities. Notably, 21% of these incidents involved compromised trusted relationships with third parties, and 17% were attributed to voice-based social engineering techniques, or “vishing.” Furthermore, the report identifies “malicious insiders”—employees or contractors leaking confidential information—as a growing threat, often using consumer-focused cloud storage services to exfiltrate data.
One concerning finding is that nearly half of intrusions resulted in data theft without immediate extortion attempts, indicating that attackers are adopting a stealthier approach. These incidents are marked by prolonged dwell times, allowing attackers to persist undetected within networks.
To combat these rising threats, Google Cloud Security has provided a set of recommendations for organizations to bolster their defenses. For large enterprises, the advice includes enhancing patch management protocols, implementing multi-factor authentication, and establishing comprehensive incident response plans. However, small and medium-sized businesses may lack the internal resources to effectively manage these challenges and are encouraged to seek managed service providers with relevant expertise.
As AI continues to shape the landscape of cybersecurity, the imperative for businesses to upgrade their defenses becomes increasingly critical. With AI tools transforming the tactics of cybercriminals, organizations must evolve their security strategies to keep pace. The call for automated, AI-enhanced defenses not only highlights the urgency of the situation but also underscores the broader implications of AI in both offensive and defensive capacities across digital landscapes.
See also Ransom Payments Surge to 24.3% as AI-Enhanced Cyberattacks Target Companies
Ransom Payments Surge to 24.3% as AI-Enhanced Cyberattacks Target Companies Netrust CEO Jen Capones-Tongco Urges Stronger Leadership Against AI Cyber Threats in Asia
Netrust CEO Jen Capones-Tongco Urges Stronger Leadership Against AI Cyber Threats in Asia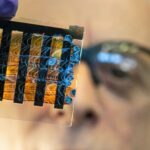 AI-Powered TwinGuard System Detects 5G Cyberattacks in Under 100 Milliseconds
AI-Powered TwinGuard System Detects 5G Cyberattacks in Under 100 Milliseconds Kaspersky Upgrades Next Platform with AI to Boost Threat Detection and Cut Costs
Kaspersky Upgrades Next Platform with AI to Boost Threat Detection and Cut Costs OpenAI Acquires Promptfoo to Enhance AI Security for Enterprise Systems
OpenAI Acquires Promptfoo to Enhance AI Security for Enterprise Systems