Cybersecurity is facing unprecedented challenges as cyber threats evolve at a rapid pace, often outpacing traditional security testing methods. As organizations increasingly operate within complex digital ecosystems that encompass cloud platforms, APIs, microservices, and rapidly deployed applications, the limitations of manual security testing have become evident. Emerging as a solution to these challenges are AI pentesting tools, which leverage machine learning and intelligent scanning techniques to identify vulnerabilities with greater speed and precision.
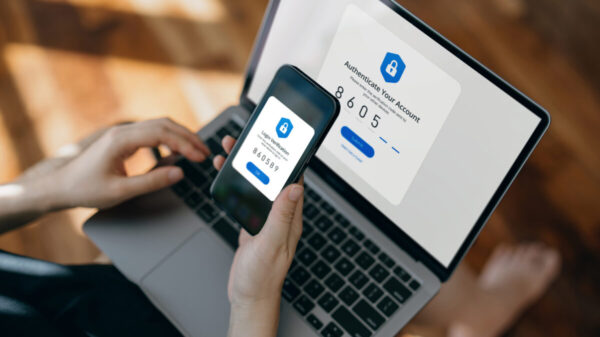
In the context of 2026, the necessity of AI-driven security testing has surged. Traditional penetration testing typically relies on manual efforts by security experts, which can be both time-consuming and limited in scope. However, the contemporary IT landscape demands ongoing monitoring and continuous testing across various environments. AI pentesting tools not only automate vulnerability discovery but also enable continuous testing, intelligent prioritization of risks, and faster detection of emerging attack patterns. This shift allows security teams to focus on significant threats while alleviating their workload.
A number of AI pentesting tools have emerged as frontrunners in this field. Among these, **AutoSecT** stands out for its comprehensive security coverage and user-friendly interface. The tool integrates advanced AI-powered vulnerability scanning and management capabilities, providing tailored solutions across diverse industry needs. Its AI-agentic Network Scanner utilizes Retrieval-Augmented Generation (RAG) to deliver precise vulnerability detection, ensuring that organizations can keep pace with evolving threats.
Another notable tool is **Escape**, which employs AI agents to automate penetration testing. This platform conducts ongoing security assessments that help identify complex business-logic flaws and provides proof-of-exploitability alongside detailed remediation guidance. By integrating seamlessly into developer workflows and CI/CD pipelines, Escape aims to enhance testing scalability while reducing costs.
**Terra Security** distinguishes itself with its agentic platform that combines automation with human oversight to simulate real attacker behavior. This synthesis enables continuous testing and validation of vulnerabilities, yielding exploit-validated findings and actionable remediation guidance tailored for modern development environments. Similarly, **Hadrian** focuses on identifying exploitable vulnerabilities across an organization’s external attack surface. Its automated processes help quickly detect new exposures and prioritize critical vulnerabilities, enabling prompt remediation actions.
Lastly, **Acunetix** specializes in web application security testing and is designed to identify vulnerabilities in websites, web applications, and APIs. Utilizing advanced crawling and proof-based scanning technologies, Acunetix offers high accuracy in vulnerability detection and provides actionable remediation guidance, thus fortifying organizations’ web security postures.
As organizations navigate the intricate landscape of digital security, selecting the right AI pentesting tool is crucial. Factors such as infrastructure coverage, automation capabilities, and integration with existing workflows must be carefully evaluated. The range of assets an AI pentesting tool can assess is vital, especially when dealing with interconnected components like web applications, APIs, and cloud services.
A robust AI pentesting tool should automate various processes, ensuring that security testing is not only regular but also efficient. This continuous monitoring allows organizations to address vulnerabilities proactively, especially after significant updates or changes within their infrastructure. Accuracy in vulnerability detection is another essential factor; organizations need to minimize false positives to focus their efforts on genuine threats.
The landscape of cybersecurity is evolving, and AI pentesting tools have emerged as a critical component in this transformation. By harnessing advanced technology, organizations can enhance their security posture and better protect their digital assets from increasingly sophisticated cyber threats. Choosing the right solution not only addresses existing vulnerabilities but also aligns with broader security strategies, ensuring ongoing resilience in an ever-changing threat landscape.
See also 20 Indian AI-Driven Cybersecurity Startups Transforming Digital Defense Landscape
20 Indian AI-Driven Cybersecurity Startups Transforming Digital Defense Landscape CrowdStrike’s Outage Sparks 20% Drop; 7 Cybersecurity Stocks to Watch in 2026
CrowdStrike’s Outage Sparks 20% Drop; 7 Cybersecurity Stocks to Watch in 2026 SISA CEO: Effective AI Use Can Deter Cyberattacks Amid Rising Threats
SISA CEO: Effective AI Use Can Deter Cyberattacks Amid Rising Threats FAI Seeks Research Fellow in Cybersecurity & AI Policy with $130K Salary and Benefits
FAI Seeks Research Fellow in Cybersecurity & AI Policy with $130K Salary and Benefits