Governments worldwide are rapidly advancing digital sovereignty mandates amid escalating geopolitical tensions, increased artificial intelligence (AI) regulation, and rising fears over cross-border data vulnerabilities. However, many public sector organizations struggle to establish a clear operational framework to assess their actual control over cloud infrastructure, encryption keys, and AI systems. New insights from Info-Tech Research Group indicate that a structured prioritization of sovereignty pressures, combined with governance alignment, can transform these mandates into a catalyst for modernization, thereby enhancing the resilience of government institutions and services.
Digital sovereignty has evolved from a policy discussion into an operational imperative for national and subnational governments, particularly as leaders face pressure to assert jurisdiction over data and technology while ensuring service continuity. According to Info-Tech Research Group, numerous public sector IT organizations lack comprehensive visibility into vendor control of encryption keys, cross-border data flows, and potential exposure to extraterritorial legal claims. Such deficiencies pose significant risks to achieving sovereignty goals, potentially undermining operational integrity and legal standing.
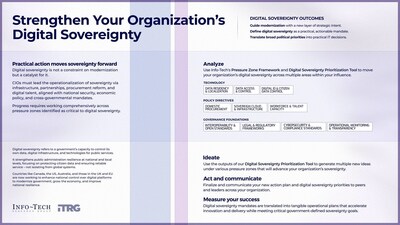
Info-Tech’s Strengthen Your Organization’s Digital Sovereignty blueprint provides a phased framework aimed at public sector CIOs to evaluate their exposure, benchmark against global standards, and translate mandates into actionable strategies. The report emphasizes that achieving sovereignty does not necessitate total isolation from global technology ecosystems. Instead, leading jurisdictions effectively integrate domestic governance frameworks with certified sovereign cloud models, contractual safeguards, and structured oversight mechanisms.
Nevertheless, many organizations find it challenging to align procurement policies with their technical architecture, clarify ownership between governmental agencies, or track where sensitive data resides and is accessed. Without that clarity, efforts toward digital sovereignty risk becoming merely aspirational rather than operational.
“Digital sovereignty is ultimately about strengthening resilience and enforceable control,” said Andy Best, Research Director at Info-Tech Research Group. “Without clear jurisdictional boundaries and accountable ownership, governments risk discovering their exposure only when disruptions or legal challenges arise. We are witnessing a discernible shift where government leaders are no longer questioning the importance of digital sovereignty; instead, they seek industry-leading frameworks that facilitate immediate operational action.”
To transition from policy intentions to operational control, Info-Tech’s framework outlines a structured, four-phase approach tailored for CIOs and senior technology leaders across IT, Legal, Procurement, and Policy functions. The first phase involves defining the scope of sovereignty and assessing current control levels. CIOs and cross-functional teams clarify applicable mandates and inventory existing controls over data residency, encryption keys, infrastructure hosting, and AI systems to identify potential exposure points.
In the second phase, IT and policy leaders benchmark against international frameworks and best practices to understand how peer governments balance modernization with control, thereby contextualizing their risk posture. The third phase utilizes the Digital Sovereignty Prioritization Tool, allowing technology and risk teams to map vendor dependencies, cross-border data transfers, and control gaps, resulting in a visual heat map that ranks high-impact sovereignty risks.
Finally, in the fourth phase, executive sponsors convert prioritized findings into a governed sovereignty roadmap comprising sequenced initiatives with clear ownership, timelines, and oversight mechanisms. This ensures that sovereignty considerations are integrated into cloud strategy, AI governance, procurement reform, and modernization initiatives.
When treated solely as a compliance issue, digital sovereignty can become a liability. However, when embedded into modernization planning, it significantly enhances long-term control and operational continuity. Info-Tech’s framework assists governments in embedding sovereignty directly into decisions regarding cloud infrastructure, AI, and data management, ensuring that priorities remain resilient through political and policy transitions.
For exclusive insights from Info-Tech’s experts, including Andy Best, and full access to the Strengthen Your Organization’s Digital Sovereignty blueprint, interested parties are encouraged to reach out via email at [email protected].
About Info-Tech Research Group: Info-Tech Research Group is recognized as one of the fastest-growing research and advisory firms globally, serving over 30,000 IT, HR, and marketing professionals. The firm delivers unbiased research and advisory support aimed at assisting leaders in making strategic and informed decisions. For nearly three decades, the company has partnered with teams to provide actionable tools and expert guidance to achieve measurable results.
See also Mexico Expands AI Use in Government Services Amidst Major Regulatory Gaps and Risks
Mexico Expands AI Use in Government Services Amidst Major Regulatory Gaps and Risks Amazon Ordered to Explain AI Use in Class Action Error, Raises Compliance Concerns
Amazon Ordered to Explain AI Use in Class Action Error, Raises Compliance Concerns Pentagon Bans Anthropic After AI Ethics Dispute Ahead of Iran Strikes
Pentagon Bans Anthropic After AI Ethics Dispute Ahead of Iran Strikes