As enterprises increasingly grapple with cybersecurity threats, the challenge of sifting through thousands of alerts generated by traditional detection tools has become a pressing concern for security teams. These generic systems often produce a cacophony of low-value alerts, forcing analysts to spend hours chasing noise while attackers exploit vulnerabilities and maneuver laterally within networks using valid credentials and trusted tools. In this context, AI-driven threat detection emerges as a promising solution, yet not every “AI-powered” platform meets the demands of enterprise environments. True cyber resilience, as experts suggest, hinges on the ability to detect threats rapidly, contain them efficiently, and minimize the operational impact of security breaches.
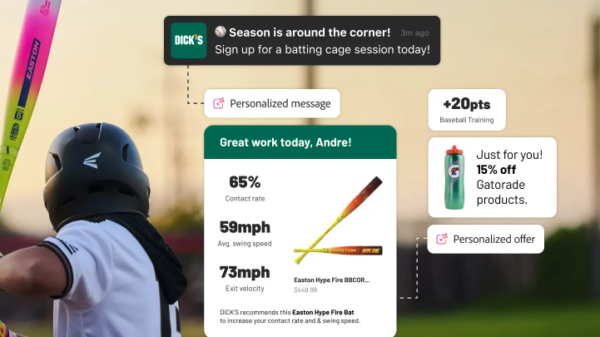
One of the primary advantages of AI detection technology is its role in reducing the noise generated by traditional systems. Conventional, rule-based detection methods are limited to identifying known threats, which can lead to inefficiencies when attackers deploy stolen credentials or legitimate admin tools. The absence of obvious malicious indicators means alerts either fail to trigger or inundate analysts with constant notifications lacking vital context. AI-driven detection addresses this shortfall by establishing behavioral baselines across users, endpoints, identities, and cloud workloads. It identifies deviations from these norms, thereby distinguishing genuine threats from benign activities.
This shift is crucial for enterprise-scale operations because legitimate administrative actions can resemble malicious behavior without a clear context. In hybrid environments, fragmented telemetry complicates the correlation of events, leaving lean security teams unable to connect the dots across disparate systems. Platforms such as Adlumin MDR™ utilize behavioral models and automated triage to filter out low-value alerts, enabling analysts to concentrate on significant incidents. The result is fewer alerts with enhanced context and prioritization, which can diminish analyst fatigue and expedite detection. From a resilience standpoint, this translates to quicker threat identification, affording attackers less opportunity to escalate their activities or access critical systems.
Moreover, correlation and automated triage capabilities within AI-driven systems are vital for limiting the blast radius during an attack. Most serious security incidents are not singular events, but rather a series of seemingly innocuous actions that coalesce into a significant threat when viewed in conjunction. For instance, a failed login attempt may seem trivial alone, but when linked with unusual file access, unexpected VPN sessions, and new processes initiated on a server, it reveals a more alarming situation. AI detection systems enhance this process by aggregating signals from endpoints, identity providers, networks, and cloud services, converting weak signals into actionable intelligence before analysts even see the alerts.
Automated triage further enhances this capability by enriching alerts with investigative context, suppressing routine activities automatically, and triggering response protocols when risks exceed predefined thresholds. This automation is crucial in fast-moving attacks, as early containment can significantly reduce lateral movement and prevent incidents from escalating into major disruptions. It is in this context that managed detection and response (MDR) services truly enhance cyber resilience—not merely by detecting threats, but by compressing the timeline between intrusion and containment.
However, effective threat detection is just one component of a comprehensive cyber resilience strategy. Enterprises must adopt a holistic approach that encompasses preparation, detection, and recovery. A robust framework includes proactive measures such as patching, vulnerability management, endpoint hardening, and DNS filtering to minimize exposure before an attack occurs. During an incident, AI-driven MDR systems play a critical role in detection and containment, while post-attack recovery solutions, like Cove Data Protection™, provide isolated cloud backups, flexible recovery options, and ransomware rollback features that are vital during periods of significant downtime.
Ultimately, AI threat detection’s effectiveness is contingent upon its integration within a broader resilience model that spans the entirety of an enterprise’s security strategy. It is essential for IT security leaders to recognize that enhancing cyber resilience involves not only minimizing noise during detection but also ensuring that responses are swift and recovery capabilities are in place when needed. The transition towards AI-driven solutions must be thoughtfully designed to meet the unique demands of modern enterprises, ensuring that detection, correlation, automation, and human expertise work cohesively to create a fortified security posture.
As AI continues to reshape the cybersecurity landscape, understanding how these technologies can be effectively harnessed will be critical for organizations aiming to enhance their resilience against an ever-evolving array of threats.
See also Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism
Anthropic’s Claims of AI-Driven Cyberattacks Raise Industry Skepticism Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage
Anthropic Reports AI-Driven Cyberattack Linked to Chinese Espionage Quantum Computing Threatens Current Cryptography, Experts Seek Solutions
Quantum Computing Threatens Current Cryptography, Experts Seek Solutions Anthropic’s Claude AI exploited in significant cyber-espionage operation
Anthropic’s Claude AI exploited in significant cyber-espionage operation AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks
AI Poisoning Attacks Surge 40%: Businesses Face Growing Cybersecurity Risks