Just three days after the disclosure of a critical pre-authorization remote code execution (RCE) vulnerability in the Marimo Python notebook platform on April 8, 2026, threat actors began actively exploiting this flaw. Tracked as CVE-2026-39987, the vulnerability allows unauthenticated attackers to obtain a full interactive shell, enabling them to execute arbitrary system commands without requiring credentials. According to the Sysdig Threat Research Team (TRT), attackers are utilizing this vulnerability to deploy a previously undocumented variant of the NKAbuse malware, which is being hosted directly on Hugging Face Spaces.
The swift weaponization of this vulnerability underscores a concerning trend of targeting artificial intelligence and machine learning (AI/ML) infrastructure. Between April 11 and April 14, 2026, Sysdig researchers recorded 662 exploit events originating from 11 unique IP addresses across 10 countries. The attacks escalated quickly, evolving from simple RCE verification to complex, multi-hour interactive sessions, suggesting a high level of sophistication among the attackers.
After compromising the Marimo platform, the attackers demonstrated structured playbooks, with aggressive credential harvesting emerging as the most common behavior observed by Sysdig TRT. They systematically extracted environment variables to steal critical assets such as AWS access keys, OpenAI API tokens, and database connection strings, which they could resell or use later for further attacks. In cases where direct reverse shell attempts were unsuccessful, attackers effectively pivoted to lateral movement using the harvested credentials.
Sysdig TRT documented various sophisticated techniques employed by different operators. For instance, one operator in Germany managed to connect to a PostgreSQL honeytrap using leaked credentials, quickly enumerating schemas, tables, and server configurations. Another attacker executed parallel connections across all 16 Redis databases, successfully enumerating and dumping every key, including session tokens and cache data. When firewalls impeded outbound network connections, operators employed DNS-based confirmation techniques to verify their remote code execution efforts.
The most alarming discovery during this campaign was the deployment of an advanced malware payload through a typosquatted Hugging Face Space named “vsccode-modetx.” By utilizing a trusted platform with a clean domain reputation, the attackers effectively bypassed traditional security monitoring and URL filtering mechanisms. According to Sysdig research, this malicious Hugging Face Space served solely as a static file hosting service for a shell script dropper that delivered a new variant of the NKAbuse malware.
This Go-based backdoor utilizes the NKN blockchain for command-and-control (C2) communications, rendering it highly resilient against conventional takedowns. Key technical aspects of the malware deployment include deceptive naming; the payload is referred to as “kagent,” deliberately mimicking a legitimate Kubernetes AI agent tool to blend seamlessly into developer environments. The malware also establishes silent persistence across both Linux and macOS systems, using systemd user services, crontab entries, or macOS LaunchAgents.
The rapid exploitation of the Marimo vulnerability and the sophisticated methods of lateral movement signal a potentially transformative moment in cyber threats targeting AI infrastructure. As the integration of AI and machine learning continues to evolve in various sectors, the implications of such vulnerabilities could extend far beyond immediate financial loss. Organizations must strengthen their security postures and vigilance against these emerging threats, especially as attackers increasingly leverage trusted platforms to mask their malicious activities.
See also Ray-Ban and Oakley Meta AI Glasses Launch in Singapore Starting at S$629
Ray-Ban and Oakley Meta AI Glasses Launch in Singapore Starting at S$629 OpenAI Reveals Insights on $10B Artificial Intelligence NPC Market Growth Through 2033
OpenAI Reveals Insights on $10B Artificial Intelligence NPC Market Growth Through 2033 Wall Street Remains Bullish on Microsoft as Stock Drops 23% Amid AI Rotation
Wall Street Remains Bullish on Microsoft as Stock Drops 23% Amid AI Rotation OpenAI Launches New ChatGPT Model with Fewer Restrictions, Heightened Cybersecurity Focus
OpenAI Launches New ChatGPT Model with Fewer Restrictions, Heightened Cybersecurity Focus Google DeepMind Assembles Team to Enhance AI Coding Models Amid Anthropic Competition
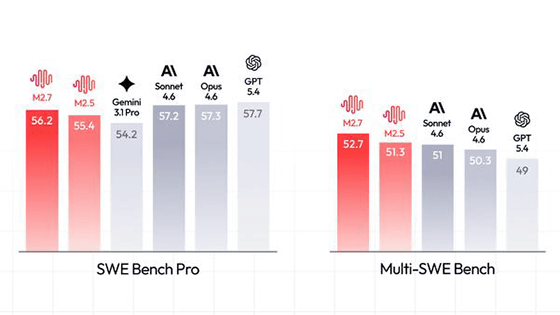
Google DeepMind Assembles Team to Enhance AI Coding Models Amid Anthropic Competition